In 1999 Change Management was all about ‘Good Housekeeping’ and Backups. Ethernet on the shop floor was in its infancy, Engineers and IT didn’t talk, Operational Technology (OT) didn’t exist and a comprehensive disaster recovery plan was having Thunderbirds number on speed-dial.
That might seem a little exaggeration, but when I heard stories such as major utility needing to contact the owner of a defunct System Integrator to get a PLC program from his attic, it did make you think….
Early Adoption
The adoption of Ethernet as the network of automation connectivity for data acquisition, was the key to closing the loop of Change Management. No longer did we have to hope that the PLC backups on the server were the latest, we checked they were, every night with automated scheduled compares. Early adopters of Ethernet such as Automotive, Airport Baggage Handling and Fast Moving Consumer Goods (FMCG) manufacturers saw the advantage of Change Management software and guarantee of having latest software copies.
They of course suffered the biggest potential downtime losses, so it was a no brainer and not surprisingly they were some of our first customers.
Open Standards
The PLC vendors were reluctant to add Ethernet options, as everyone knew the low price of components and they were all pushing their own proprietary network connectivity solutions. To accelerate the number of PLCs connected to Ethernet, MAC Solutions were one of the first to introduce Ethernet Device Servers to the market under the slogan ‘Evolution not Revolution’.
Existing PLCs could be connected to Ethernet via their serial programming ports, not only for programming software connectivity, but as it turned out more importantly for data acquisition and the OPC (Open Platform Communication - formally OLE for Process Control) revolution, which had just started.
For a long time the production/process network was separate from business/corporate network, but that could never last with the obvious benefits for management of knowing accurate real-time production data. Connecting the two networks opened a Pandora’s Box of issues that we are still coming to terms with today.
Industry 3.0
The architecture for Change Management systems changed when the two networks joined and what some might have described as the ‘Wild West’ of production networks were brought into the world of IT rules. Standalone ’islands’ of Automation with duplicate IP addresses gave everyone a headache and stopping 24/7 production to reconfigure needed serious justification for the benefits.
Connecting to the Automation layer brought its own problems with legacy devices and operating systems that could not be easily updated or patched giving network administrator’s nightmares. We’re still seeing much of this today in 2021 and with the advancement of technology and adoption of digitalization, this will be continuous journey for many!
Different Stokes
Forcing IT policies into the Automation layer was always going to end in tears. Engineers needed Admin rights and updating systems to support latest PC and network standards was either impossible or work required prohibitively expensive. When you have seen a major manufacturers Automation network connected directly to an ADSL router to give internet access for Engineers without IT’s knowledge, you know it will end it tears….. and so OT Cyber Security was born and Change Management became an integral part of any companies Cyber Security strategy.
Keeping your house in order
The ‘good housekeeping’ of keeping backups and knowing who did what, where, when and why, hasn’t gone away, but with the now critical importance for a company to have a Cyber Security strategy, Change Management Software has matured.
Whether it is a malware attack, finger trouble or just a plain old hardware failure, having a good Disaster Recovery Procedure is critical to ensure a timely restoration of system operation. Regular automatic compares and backup on difference ensures that the latest version is safely stored and ready to be deployed immediately.
Change Management Software can also help with a Stuxnet like attack, by detecting additional code added to PLCs and SCADA Systems. Additional features such as reporting on PLC Hardware/Firmware versions deployed all help with the identification of weaknesses in Cyber Security.
Legislation
The Network and Information Systems (NIS) Directive has forced Utilities, transportation companies and others to evaluate their Automation systems for Cyber Security issues and Change Management plays its part working towards the required compliance especially in Objective B, Principles B2, B3, B4 and B5.
SolutionsPT and our sister company MAC Solutions has an unrivalled offering with Cyber Security Products specifically designed for the OT layer. We understand that legacy devices are often in operation past their supported lifespan and run at risk. While you can often obtain second-hand hardware, what you cannot replace is the data. If this data was lost, could you ever recover?
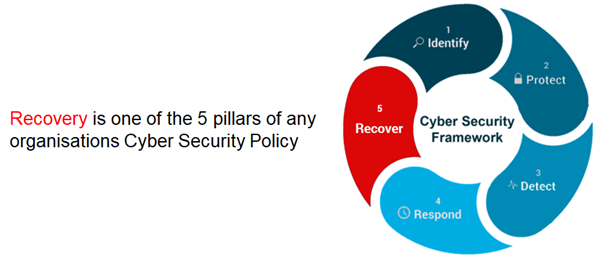
Change Management is just one part of a fully integrated Cyber Security Solution. If you do nothing else to protect your OT assets (and we would strongly advise from not taking this approach) then make sure you can recover from unintentional data loss for your critical assets.
See how simple data protection can be by viewing our latest webinar:


