I am often asked by customers “what is the best way to protect my OT environment from cyber security threats?” There is no single answer or step which will deliver a robust operational environment. Defence strategies must be layered, delivered in depth and first and foremost, you must understand what you need to protect. If the question was re-phrased to say, “what is the most cost-effective tool to deploy to protect my OT environment?” then I would say Endpoint Protection.
Research by IDC concludes that 70% of all breaches start with the Endpoint, whilst TechRadar highlights that 90 percent of data breaches are caused by human error. The risk of an endpoint acting as a point of presence and the ‘accidental insider threat’ is one of the largest risk factors to consider for any operational environment.
Live Long and Prosper
In January 2020 Windows 7 and Server 2008R2 became end of support by Microsoft. While there was a large push within IT sectors to remove the legacy operating system, the same adoption within OT has been much slower. The need to upgrade is often driven by factors other than security, such as business efficiencies. We have discussed this in our recent blog “Are your industrial systems ready for today? It's time to evolve”
Fast and Furious
While there are security concerns with legacy operating systems, what is often overlooked is the support gap that is also present within Windows 10. In early 2018, Microsoft announced Windows Lifecycle which introduced a semi-annual refresh of products with a much shorter lifespan.
Customers who are running Windows 10 Professional versions 1507 through to 1803 (6 versions in total) are no longer receiving monthly security updates unless they upgrade to 1809 or greater. This change complicates OT operations, moving from a 10+ years lifecycle to 18 months has significant effects for OT stability as well as long term security.
As security and OT professionals, we need to take a step back, view how this affects our assets and make security decisions that are aligned to OT environments. The IT model of fast adoption and rapid upgrade is not a one size fits all.
Network and Information Security Directive (NIS-D)
Our attendance at CyberUK and Infosec highlighted a common challenge faced between Operators of Essential Services (OES) in addressing NIS-D compliance. The common pain points focused on 2 key principles of the directive:
- C1 – Security Monitoring
- C2 – Proactive Security Event Discovery
The inability to effectively identify security incidents, identify system abnormalities for attack detection and be proactive in attack discovery was a systemic problem faced by many. SolutionsPT provide a solution to address this need for network monitoring through Claroty. Re-focusing on the endpoint, this sets us a challenge to address this need for our OT customers at the endpoint.
Thinking Differently
Endpoint protection is a wholly accepted practice within IT and broadly accepted within OT operations. Absolute security concludes that 28% of endpoints have missing AV or signatures that are out of date. Signatures assume that a threat has been seen before and someone has to be patient zero for the threat to be identified.
Deploying updates to the endpoint takes time, effort and creates micro changes to the operational environment which may introduce instability, especially if the update includes modifications to the core protection application.
At SolutionsPT we've been rigorously testing Artificial Intelligence (AI) security products from Blackberry Cylance which we believe address the security needs of the OT environment. These tools help achieve a robust level of security, reduce workloads for OT engineers and help deliver regulatory compliance within NIS-D and other OT/IT security frameworks.
CylancePROTECT is an integrated threat prevention solution that combines the power of AI to block malware infections with additional security controls that safeguard against script-based, fileless, memory, and external device-based attacks.
CylanceOPTICS is an endpoint detection and response (EDR) solution designed to extend the threat prevention delivered by CylancePROTECT by using AI to identify, report and prevent widespread security incidents.
Endpoint Protection that Works for OT
While the security needs for IT and OT endpoints are broadly aligned, there are several key differences that need to be addressed to be highly effective on the plant floor. These have been identified by our customers as:
- Having low resource utilisation on the host
- Require minimal maintenance and updating
- Be effective on ‘air gapped’ and ‘partially connected’ networks
- Provide protection to current and legacy systems
- Protect against known and unknown threats
- Identify root cause analysis
- Compensate for operating systems and applications that are no longer being patched
- Restrict and control the use of removable media accessed on OT assets
- Have the ability to interface with enterprise event collection tools
CylancePROTECT provides the right balance of features needed for OT systems, these are addressed by:
- Using AI detection, this means there are no signatures to update so ideal for isolated or discrete devices. Memory usage is around 70MB and CPU resource utilisation is less than 5%
- Files are scanned only if a change is detected, threats are identified in under 200ms without ever executing the file. The use of scripts can also be managed with granular controls over memory protection, often false positives identified within OT/SCADA systems
- Windows XP through to the latest versions of Windows, Linux and Mac operating systems are protected using the same application suite delivering consistency throughout the operational environment
- CylancePROTECT can also co-exist with other antivirus vendors without conflict for defence in depth approach, ideal for highly secure environments and sensitive verticals
- USB devices management allows control over removable media and other plug and play devices
- Application controls can be activated to lock a device such as a HMI from running any additional application or operating system executable. This is ideal for devices which need to have a frozen runtime or no longer receive security updates
- Memory access is monitored to identify the presence of fileless malware, if identified the process can be alerted upon or immediately terminated stopping the spread of infection. Granular controls also take account of the way SCADA applications interact with the operating system
- CylancePROTECT can be deployed to connected, partially connected and isolated networks with reporting to enterprise event collection tools
Zero Day Protection – The Predictive Advantage
AI threat profiling gives a proven predictive advantage of up to 33 months over known, unknown, and zero-day malware. CylancePROTECT is capable of preventing threats that did not exist when the AI model was created.
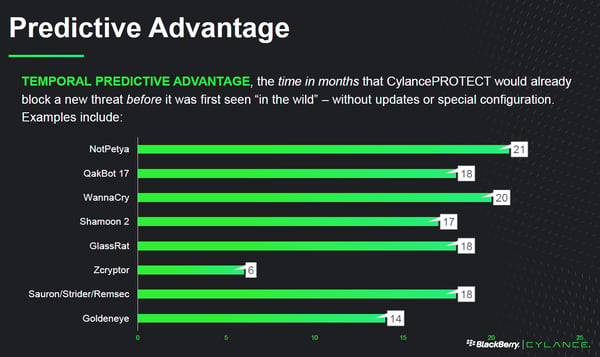
In practical terms, this indicates that regular updates to CylancePROTECT are not always necessary which is ideal for OT environments. Updates to the AI model is ongoing and generally sees releases every 6 months which better suits planned downtime and maintenance windows.
Limited connected networks can also benefit from ‘Centoids’ (mathematical threat detection models) to an internally hosted ‘Hybrid Server’, this caches realtime micro changes to the AI model providing an always up to date security solution.
SE labs undertook an independent study of CylancePROTECT predictive advantage, the report is available here:
SolutionsPT Findings
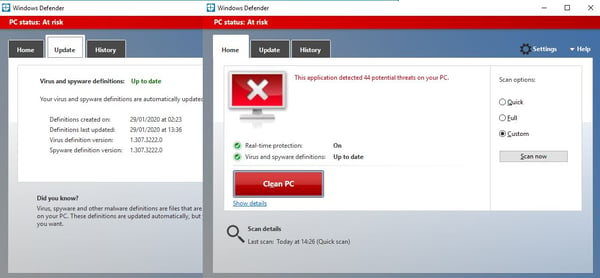
SolutionsPT security consultants obtained 101 malware samples, some which contained zero-day threats. The test was undertaken using a Windows 10 host on the 02/10/2019 using CylancePROTECT 2.0.1540.8 (Released in August 2019) and Windows Defender (1.303.659.0) which were both fully up to date. Cylance identified 101 samples as malicious and Windows Defender identified 37.
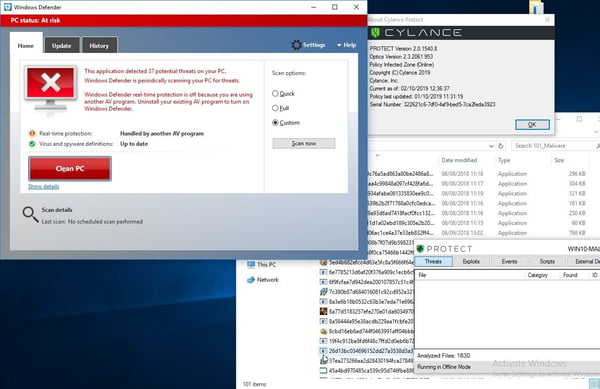
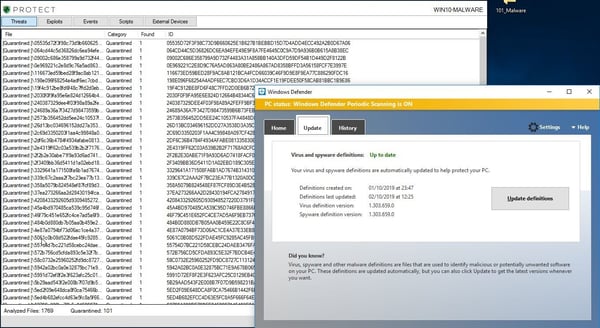
The same test was rerun on the 29/01/2020 on the same sample set, Cylance was removed from the test system and Windows Defender acted as the primary threat detection application. This time, some 4 months later, 44 samples were identified as malicious, an increase from the original 37 but still less than the 101 originally quarantined by Cylance.
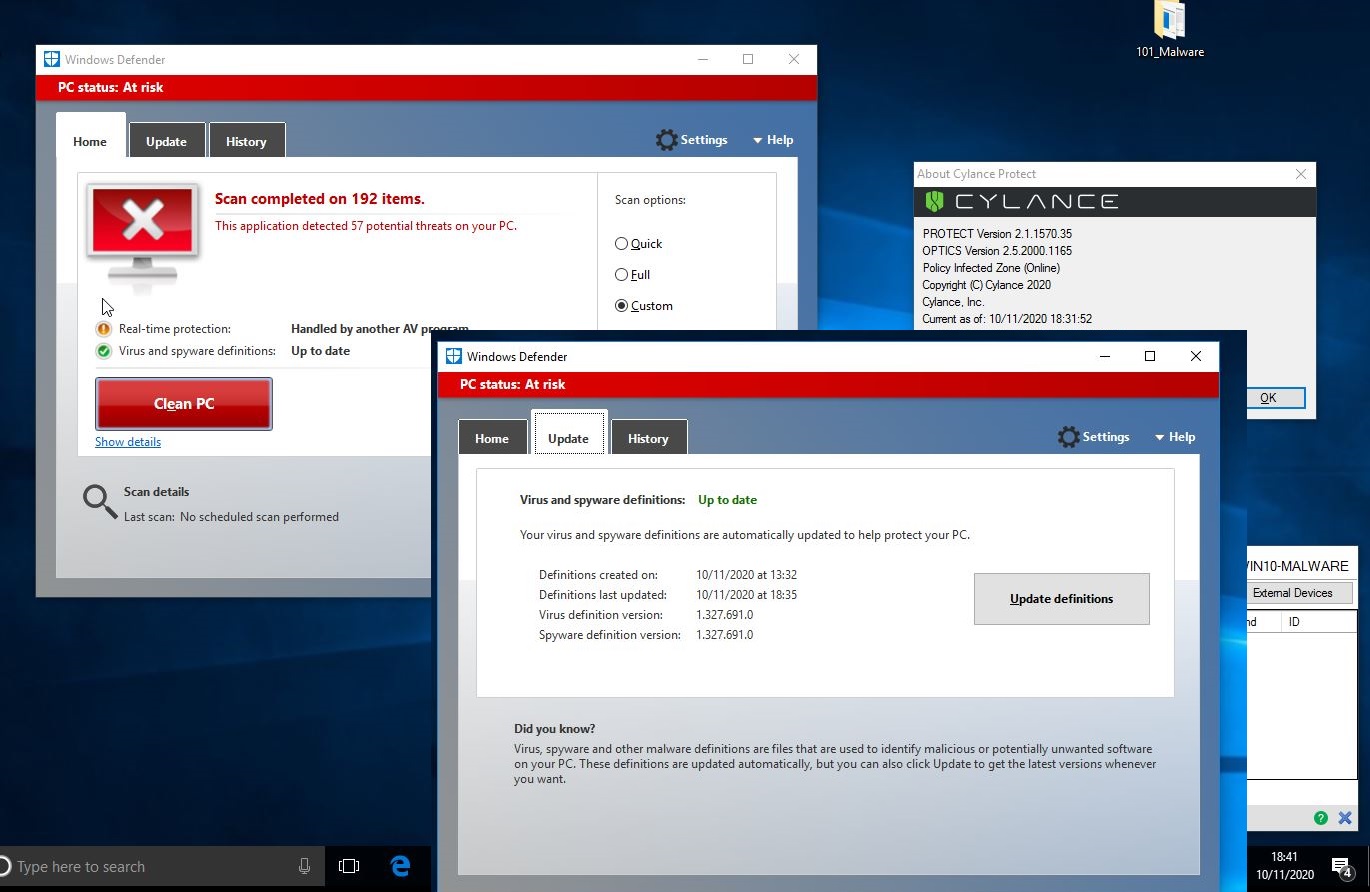
Update (revisited in November 2020)
During lockdown we did a final run on this VM, an update to Microsoft Defender on 10/11/2020 using definitions 1.327.691.0 to establish a baseline over a year later. This time the built in protection for Windows 10 managed to successfully identify 57 potential threats proving as signatures improve so does the detection rate. This is still far behind Cylance which identified all 101 of them 13 months ahead of other vendors.
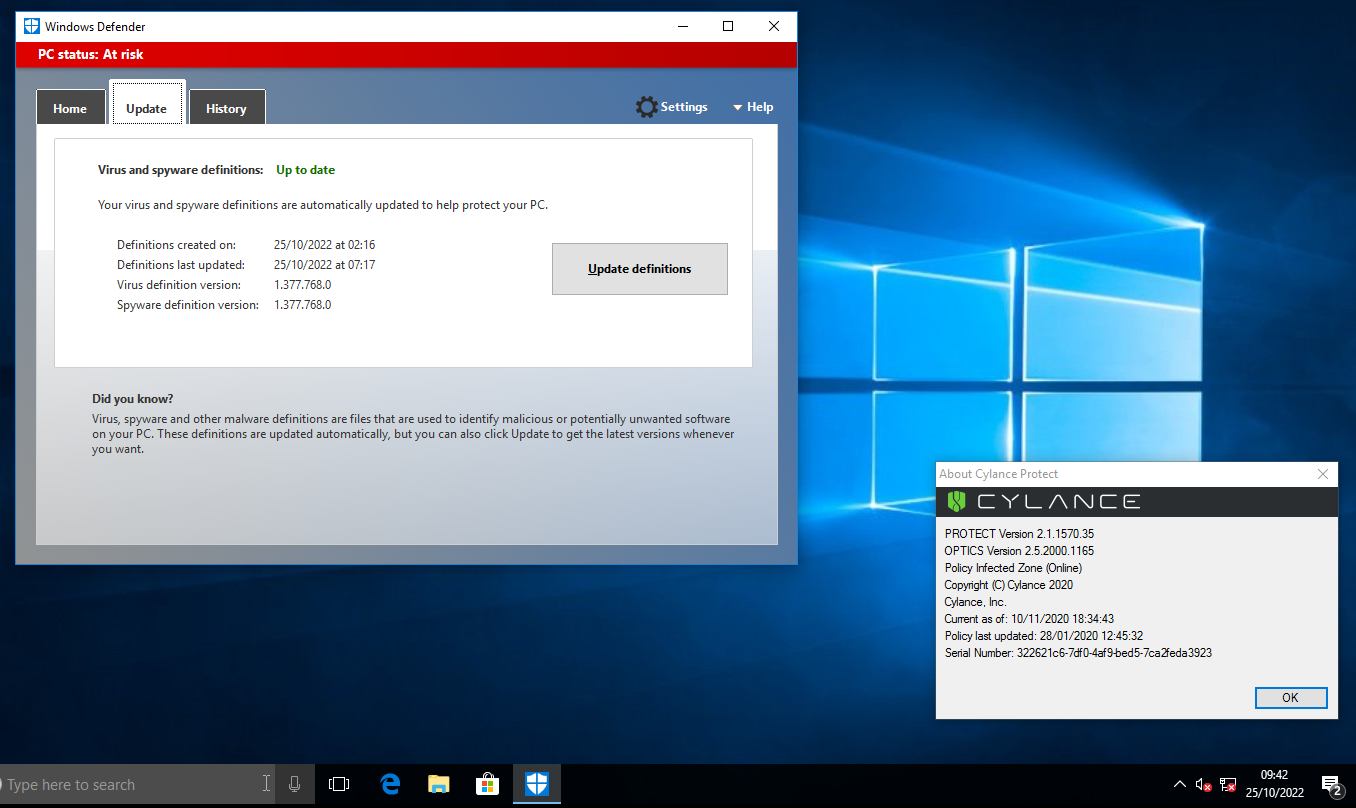
Final Update (revisited in October 2022)
Before I removed this lab I thought I was revisit this a final time, so I update to Microsoft Defender on 25/10/2022 to establish a baseline 3 years later. This time the built in protection for Windows 10 managed to successfully identify 51, so down from the 57 potential threats in 2020. This is still far behind Cylance which identified all 101 of them 36 months ahead of other vendor.

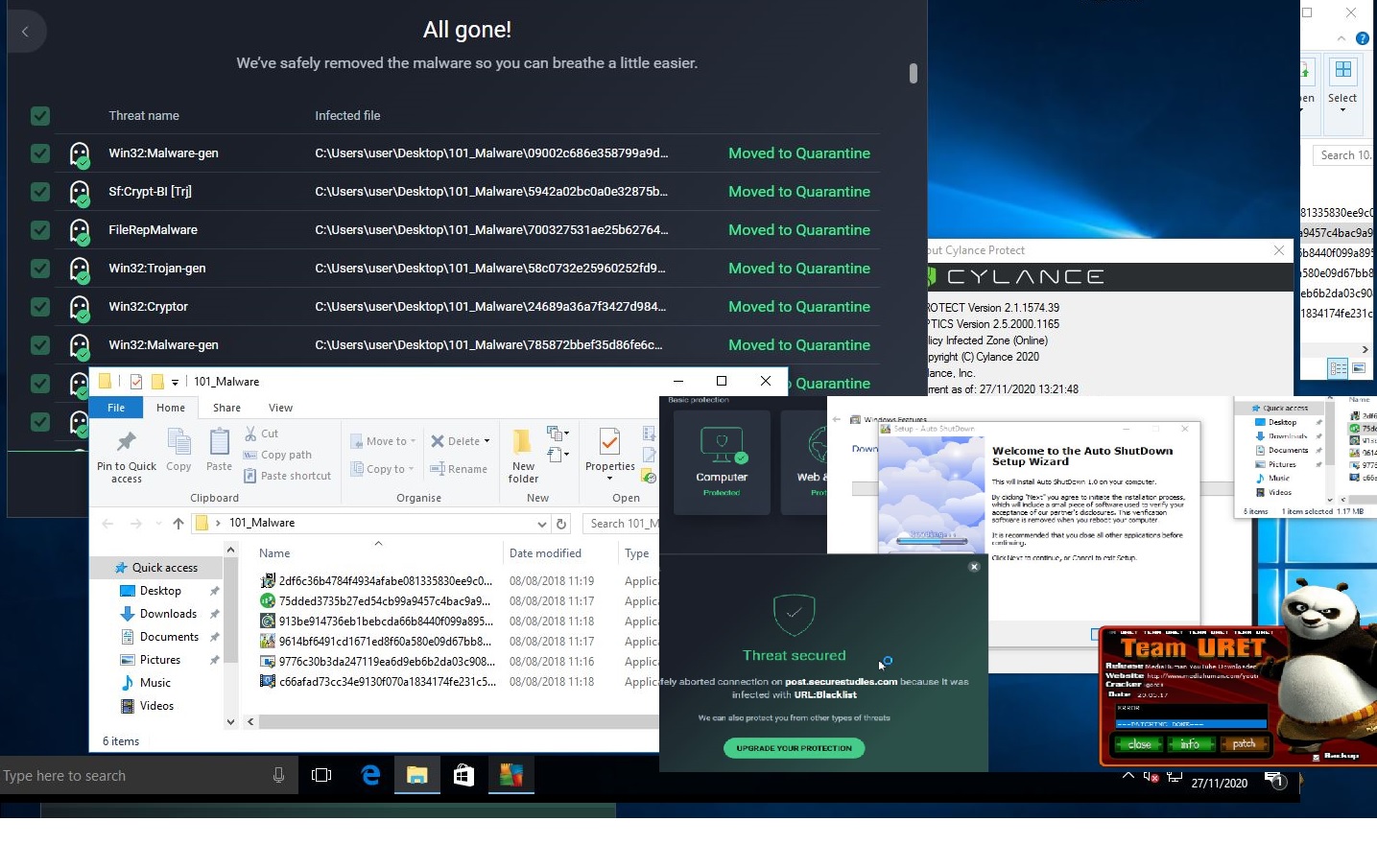
Customer Testing
One customer on the 27/11/20 who was happy with their AV solution but dissatisfied with how much time and effort they needed to invest keep their solution up to date was surprised to see that their product had only identified 95 of the 101 malware samples we tested. Detonating the remaining payloads quickly identified that they had successfully installed, one attempted to communicate with C&C servers and CPU usage was at a consistent 100% with miners running in the background rendering the machine totally unusable. During the test we could also see Ransomware payload executing, however this never fully completed and crashed out.
Putting this into perspective, we took malware samples obtained throughout 2018, tested them in 2019 and then revisited in late 2020. Some of which payloads are still bypassing traditional signature based systems.
SolutionsPT would always advise you undertaken your own testing as mileage will vary but we are seeing similar results to those identified by SE labs independent report .
Co-Exist for Defence in Depth
Cylance solutions are compatible with legacy AV products and can run on the same endpoint without conflict. Some organisations may choose to implement Cylance alongside their legacy AV to discover what their current endpoint protection is missing. This proof of concept often leads to them retiring their legacy solutions once they feel confident that Cylance can provide the protection their organisation requires.
Endpoint Detection and Response (EDR)
CylanceOPTICS deploys trained threat behaviour models directly on the endpoint which are fully aligned to the MITRE ATT&CK framework. This empowers protected devices to function as self-contained security operations centres.
CylanceOPTICS includes a configurable context analysis engine (CAE) that monitors endpoint events in near real-time. This identifies suspicious behaviour according to the device policies and detection rules. For example, send alerts or engage an automated response based on how PowerShell was called and where it was invoked, i.e. if via a web browser then automatically terminate.
CylanceOPTICS works in conjunction with CylancePROTECT to provide prevention-based security, threat hunting as well as the tool sets often required for compliance frameworks such as NIS-D and IEC 62443.
Catching Threats with AI Is Catching On
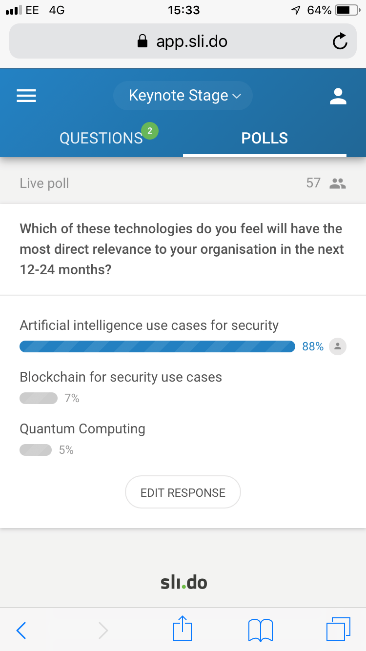
Organisations are already investing in AI for security and this will only increase. Our attendance at Infosec indicated that 88% of people polled felt that AI has relevance for security for their business. Cylance support these findings by stating “60% of the IT decision makers surveyed say they already have AI-powered solutions in place and 40% said they are planning to invest in them in the next two years”.
At SolutionsPT we closely follow security trends, attending national events and share our experience with peers. We monitor industry challenges and review innovations within the IT market, selecting best in class solutions which are suitable for OT environments. Our solutions are tested to ensure they are compatible with all the core products we offer so you can be assured they can successfully co-exist, saving you time and effort.
Cylance AI is a mature and a proven technology deployed to over 14 million devices. If you are ready to see what your legacy protection products may be missing or just want to break free of the constant upgrade cycle associated with legacy antivirus, we can provide a no obligation 30-day proof of concept. Why not let the technology speak for itself?
#solutionspt #otsecurity #otcybersecurity