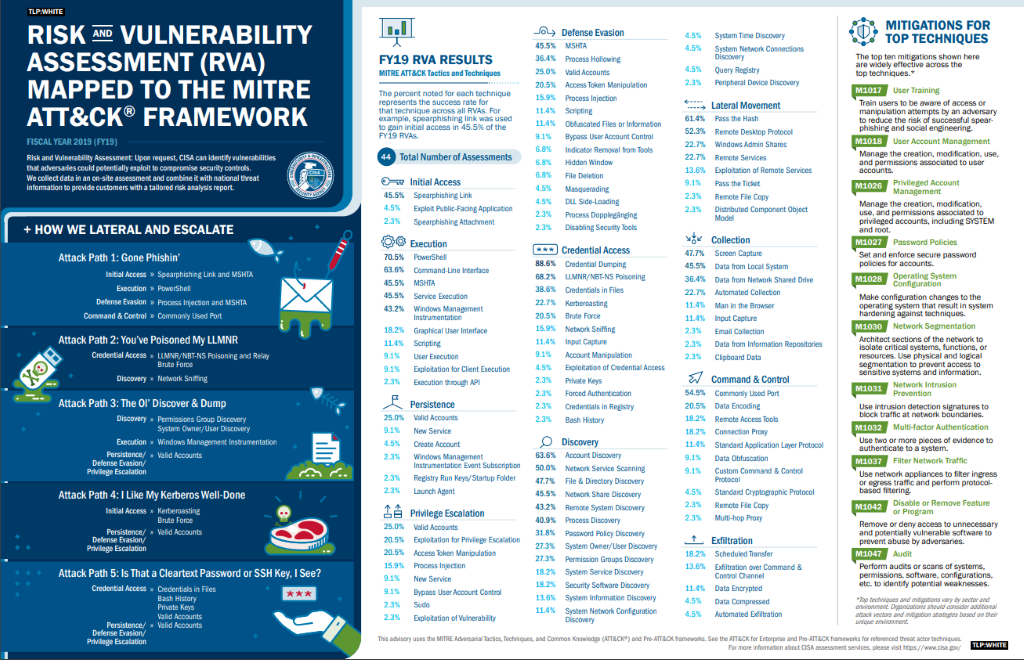
The Cybersecurity and Information Security Agency (CISA) has released an informative infographic mapping analysis of 44 of its Risk and Vulnerability Assessments (RVAs) conducted during 2019 to the MITRE Adversarial Tactics, Techniques, and Common Knowledge (ATT&CK) Framework. This details routinely successful attack paths CISA observed during assessments conducted across multiple sectors. Cyber attackers can often use these attack paths to compromise organisations.
The MITRE ATT&CK framework is a global knowledge base of adversary tactics and techniques based on real-world observations. Their knowledge is used as a foundation for the development of specific threat models and methodologies in the private sector, in government and in the cybersecurity product and service community.
 March Reboot
March Reboot
At the start of 2020, businesses had already planned where their priorities lay for the year and started to make headway into work packages and business plans. Come March, the whole world was ‘rebooted’ and received several unscheduled updates, the global pandemic has quickly taught us how to identify priorities based on the most important outcomes. It showed us that many of the activities that we considered 'priorities' before March are not really priorities at all. The fallout quickly established resilience as one of the key objectives of security programs to help businesses maintain productivity.
As we continue through this period we must work and live while continuing to select priorities that allow us to focus on our most important objectives. Assuming that a distributed workforce is the new norm the question we need to address is how to secure data, processes, and communication irrespective of where employees and third parties are located?
Back to Basics
Cybercriminals are smart but they are largely opportunistic, it hasn’t taken them long to establish that remote working has made businesses more vulnerable. In the longer term, many people are likely to remain working entirely or partially from home. This means a larger attack surface and a greater risk to operations as well as critical data.

None of these risks are new, they have always been present, but they may not have been on our radar. Being forced with the inevitable, which in many cases for OT has been to allow ‘remote access or control’, is often a daunting reality.
SolutionsPT takes a simplified approach that maps directly into the Cyber Security Framework, which forms the foundations for CISA advice and has many commonalities with other publications such as ISO 27001, IEC 62443 as well as NCSC 10 steps to Cyber Security, to mention a few.
Assessing Risks
People working in their home environment will indeed increase risks such as the secure use of collaboration tools, shared devices in the home, limited workspace and home Wi-Fi which may be poorly secured or shared with others. Organisations need to be proactive on several fronts, ranging from rethinking risk around a largely remote workforce to security and privacy trade-offs, including educating staff and raising awareness.
Adversaries are focusing their efforts now knowing that workers are no longer inside the sanctuary of a corporate firewall. Does this make us any less secure? Well, yes it does, especially if you have continued to operate the way you have always done. Remote working makes sense, but more often than not, humans are creatures of habit and like doing things a certain way and our default position is to stick to what we know. When faced with the initial crisis, we were willing to change for a short period of time, the question is how do we make these changes lasting?
Moving Forward
This is simply a question of balancing risks of security and productivity which is the foundation of all security frameworks. SolutionsPT approach is based on a ‘return to basics’ and review, establish how your business has changed in the pandemic and map this to how the threats landscape is changing linking back to MITRE ATT&CK framework. Taking a pragmatic approach, we understand and recognise that you cannot eliminate all risks. Put simply, we take risks every day, when we walk up and down the stairs there are risks of a slip, trip or fall, however that doesn’t stop us traveling using the stairs multiple times a day. This translates to looking at how data is used and where the risk is greatest.
There is likely to be a question around risk reduction and use of personal data or devices. Rather than simply imposing policies, and enforced controls, organisations should seek to build agreement with staff on what works and what doesn’t, after all, a home is not a dedicated office environment.
Ultimately, this is all about recognising that the world has been through a significant upheaval, taking a holistic informed look at how risks map on to this, and then implementing realistic, high impact, cost-effective countermeasures that allow business to operate without friction and with enhanced levels of operational security.
At SolutionsPT we closely follow security trends, monitor industry challenges and review innovations, selecting best in class solutions which are suitable for OT environments. If you’re ready to see what your legacy protection products may be missing or just want to break free of the constant upgrade cycle associated with legacy solutions, we can provide a no obligation 30-day proof of concept. Why not let the technology speak for itself and identify what others may be missing?
#solutionspt #otsecurity #otcybersecurity

