Claroty has introduced significant updates to their OT security platform and we are pleased to share them with you. With these enhancements, which include Continuous Threat Detection (CTD) version 4.1 and Secure Remote Access (SRA) version 3.0, the Claroty Platform offers the industry’s broadest set of OT security controls in a single solution.
Continuous Threat Detection 4.1 – What’s New
The product has received a total visual overhaul, the new interface is fresh and intuitive, providing extensive detailed information about assets, risks and vulnerabilities.
CTD now has the option to be cloud connectable through the Enterprise Management Console (EMC) which is strategically placed on the northbound side of the OT network, this allows threat feed data to be updated automatically, as well as highlighting peer threat and risks. When a known threat is alerted upon, it will compare that signature among other sites known to Claroty that also participate in anonymous event data to providing a reputational peer score. All data exchanges comply security and GDPR regulations if this function is enabled.
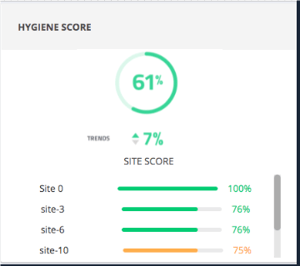 The cyber hygiene of your OT network is strategically placed on the main dashboard, this details the overall maturity of your OT network, including trends. Custom dashboards can be created for different user personas. Where multi-site deployment is implemented, this is presented as single score for all sites from the EMC.
The cyber hygiene of your OT network is strategically placed on the main dashboard, this details the overall maturity of your OT network, including trends. Custom dashboards can be created for different user personas. Where multi-site deployment is implemented, this is presented as single score for all sites from the EMC.
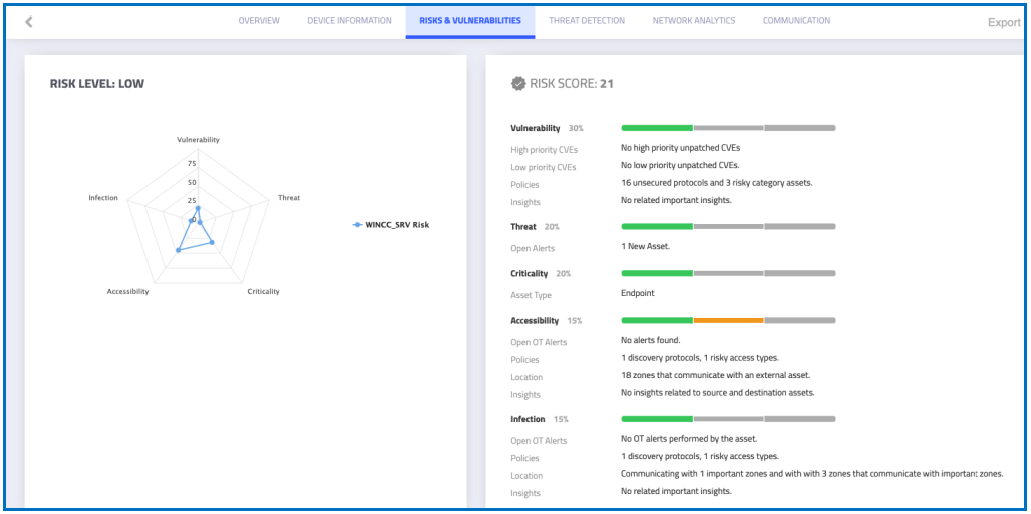
Taking a deeper dive into the assets and zones will indicate where risks are present, with details on Vulnerabilities, Threats, Criticality, Accessibility and Infections allowing for remediation work to be planned in where necessary to drive risk reduction.
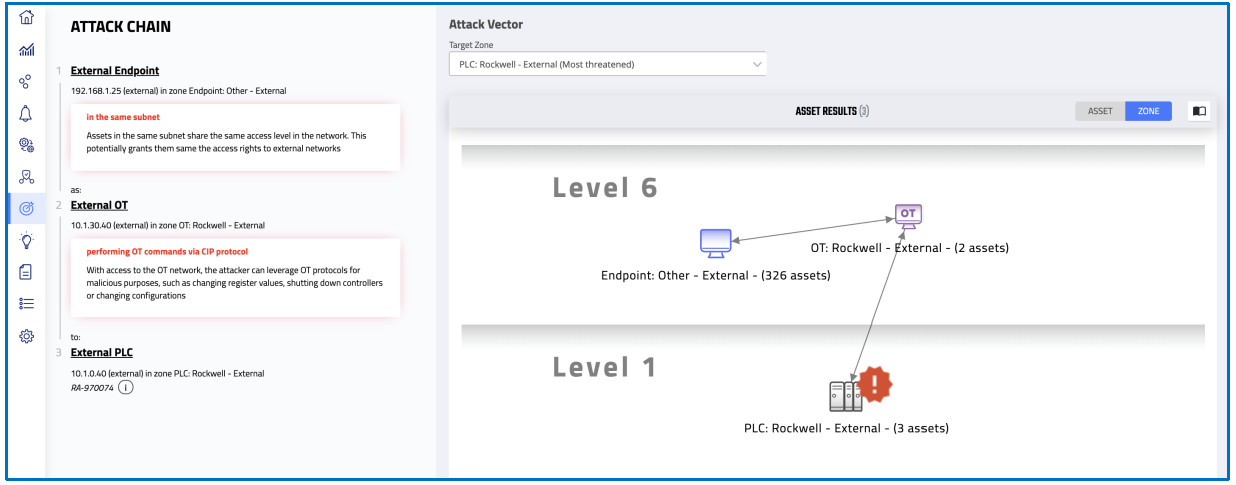
Attack Vectors
Automated Attack Vectors have been extended to work with assets as well as zones. These are automatically calculated to provide insight to how a chain of events could lead to a compromise of your system. By addressing these high-risk threats as a priority, a significant improvement to your security posture can be quickly achieved, without the risk of a penetration tester interacting with your live running system. These tests can be run at any time without affecting production.
Secure Remote Access 3.0 – What’s New
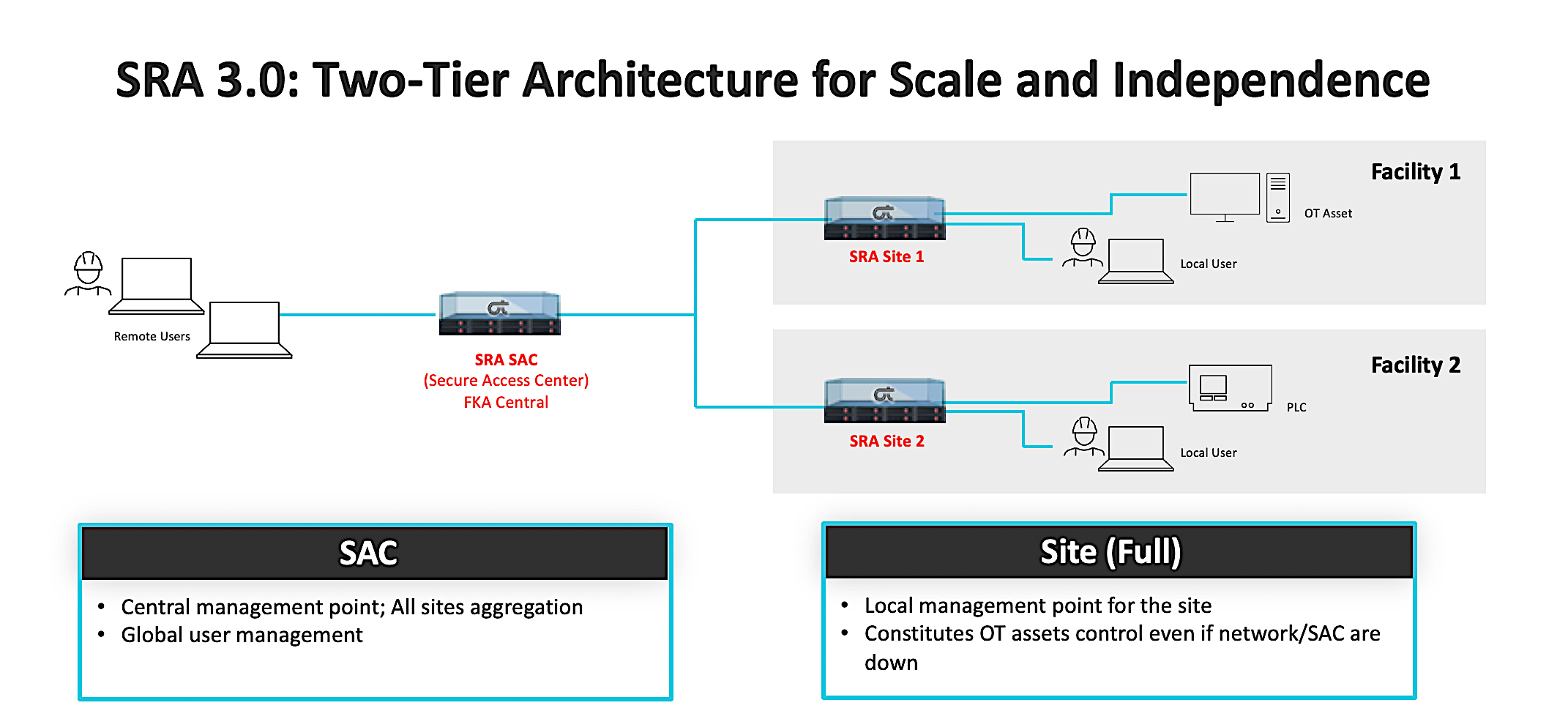
The SRA architecture has been redesigned in order to create a more scalable and efficient system. This product advancement improves the efficiency of users in the system while providing resilience in the event of single or multiple component failures.
- Independence – SRA architecture allows connection to assets from both the Secure Access Center (SAC), this component replaces what was originally the Central component. Access to assets is also possible from the SRA Site component to deliver tiered access.
- Scalability – Session distribution that improves the overall scalability and load balancing of remotely presented systems.
Remote Access session distribution for external and internal users is as follows:
- Internal users can initiate a session directly from the SRA Site towards an asset (which could only be achieved via the Central in the previous version)
- External users can initiate a session from the SAC towards an asset (as in the previous version)
The new architecture of SRA consists of the following components:
- Secure Access Center: This component is generally located at the enterprise level
- Full Site: This component is based within the operations level or OT DMZ
Claroty Platform for Complete OT Access and Security
Secure Remote Access complements Claroty’s Continuous Threat Detection (CTD) offering to deliver a complete OT security solution. The combined platform delivers the industry’s broadest set of OT security controls, including asset discovery and visibility, vulnerability management, threat detection, and segmentation policy.
With the Claroty Platform, OT and IT staff can manage risk in their OT environments with minimal training and no disruption to infrastructure and security workflows.
We have only just scratched the surface of the features of CTD 4.1 and SRA 3.0.
SolutionsPT are Claroty preferred partner in the UK and Ireland, with over 30 years experience delivering industrial solutions to over 2000 critical businesses. If you are affected by the inability to satisfactorily monitor or remotely access your operational assets, or if you would like to discuss the next steps for a proof of concept then please get in touch.

