The US National Institute of Standards and Technology (NIST) is planning significant changes to its Cybersecurity Framework (CSF), the first in five years, and the biggest reform yet.
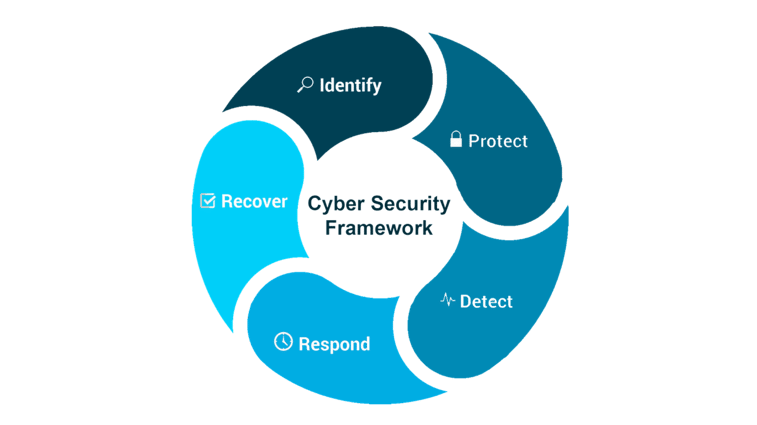
This framework was first published in 2014 and updated to version 1.1 in 2018, the CSF provides a set of guidelines and best practices for managing cybersecurity risks. The framework is designed to be flexible and adaptable rather than prescriptive and is widely used by organisations and government agencies to create cybersecurity programs and measure their maturity.
It is a firm favorite of SolutionsPT as this addresses the needs of both IT and OT equally and further supports the more widely adopted IEC 62443-x framework, addressing many shortfalls.
Following a long consultation, NIST has published a consultation paper for CSF 2.0 and opened it up to further review until the 3rd of March 2023. The resulting feedback will be used to develop a final draft of the revised framework, due out sometime this summer. Contact cyberframework@nist.gov if you would like NIST to consider participating at a conference, webinar, or informal roundtable to discuss the CSF update and this paper.
“We think that there's been enough changes in the cybersecurity landscape to warrant a significant update this time around," says Cherilyn Pascoe, senior technology policy advisor at NIST and Cybersecurity Framework Program lead.

Addition of Governance
The new CSF 2.0 will include a new “Govern” Function to emphasise cybersecurity risk management governance outcomes. While the five CSF Functions have gained widespread adoption in national and international policies, including ISO standards, NIST believes that there are many benefits to expanding the consideration of governance in CSF 2.0.
This new crosscutting Function will highlight that cybersecurity governance is critical to managing and reducing cybersecurity risk. Cybersecurity governance may include determination of priorities and risk tolerances of the organisation assessment of cybersecurity risks and impacts, establishment of cybersecurity policies and procedures and understanding of cybersecurity roles and responsibilities.
These activities are critical to identifying, protecting, detecting, responding, and recovering across the organisation, as well as in overseeing others who carry out cybersecurity activities for the organisation, including within the supply chain of an organisation.
Risk Management
For the first time, the new framework will have a significant focus on supply chain risk management, helping and encouraging organisations to address third party risks of all kinds, from cloud computing to computers, software, and networking equipment, along with the non-technology supply chain.
Another critical area still is NIST's proposal to keep the framework technology and vendor neutral, with some calling for it to address specific topics, technologies, and applications. Revising the CSF offers an opportunity to clarify the relationship among governance and cybersecurity risk management across the CSF narrative.
The CSF 2.0 will describe how an underlying risk management process is essential for identifying, analysing, prioritising, responding to, and monitoring risks, how CSF outcomes support risk response decisions (accept, mitigate, transfer, avoid), and various examples of risk management processes (e.g., Risk Management Framework, ISO 31000) that can be used to underpin CSF implementations.
Govern was always in our security training!
Since we launched our recently NCSC assured: Applied Security for OT Engineers training, we cover the power of governance and how this is important to have in place AND the power this can have to provide secure operations. Feedback from the course indicates that OT engineers often think this is business decision to be made, not part of their role and consequently often overlooking the power of feeding up from the factory floor the needs to have security to the business, especially to the compliance, quality, or governance teams.
“By feeding back into policies and procedures, you have the vehicle and the stakeholder buy in to deliver the security programs that are required for digital transformations” says Lee Carter, SolutionsPT cyber security product manager.
“If your polices dictate your expected security baseline for example: managed switches, monitoring, endpoint security and expected control outcome such as applying port security, this provides the ability to outline what is expected and what good should always look like. This provides engineering teams the ability to address local security issues as it is pre agreed with stakeholders and expected as part of a well-managed deployment. This also feeds back into customers PQQ clearly outlining what are the expected requirements to OEM’s and integrators to ensure they are supplying systems that are secure by design.’
If you also speak to governance and the finance teams, understanding what controls are expected from the insurance underwriters may allow for cost neutral implementation of security controls which reduce insurance costs.
Why pay for cover when you can address this at source, make your operations more secure and reduce your annual premium?
Insurance Requirements
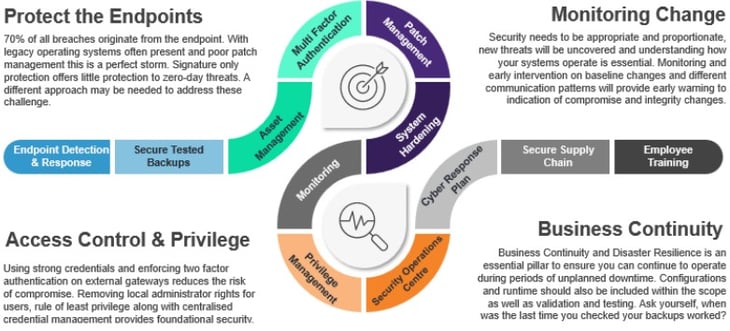
The insurance pre-requisites are becoming common place, often these questionnaires are completed with an IT focus, forgetting that over 70% of OT systems are running on IT hardware. If this forgotten world is not assessed correctly then insurance may be invalid and the cover unsuitable in the event of a claim. SolutionsPT have seen customers premiums increase by 600% or cover reduced to 10% for the same premium, simply due to the omission of a key control such as remote access or endpoint security.
Assessments
The best approach is to align to a security framework, after all, they have already done the heavy lifting for you.
We often get asked to review an architecture to ensure that it is compliant with a standard or regulation. Because most of our systems have a level of dependencies it is virtually impossible to be able to declare a part of the plant is compliant in isolation. As compliance relies on much more than the physical architecture, we would need to understand the companies cyber culture as much as the specified end point protection.
Assessments are just that, they are a snapshot in time to indicate the health and maturity of a deployment, the more detail you give the more feedback you’ll get!
Security starts at the top, is there stakeholder buy in, and if so, then do policies and procedures underpin and support this approach, as good security is all about People, Process and Technology. We recently wrote about this in a recent post Knowing where you are going is key to getting there!
Check and Balances
At SolutionsPT we take a balanced approach to the management of assets and the security throughout its lifecycle. We understand that it is not always possible to apply every element of best practice to every part of the plant floor, however by using the correct tools, frameworks, and a pragmatic approach we can offer advice and solutions that reduce risk and improves operational efficiency and security.