If you’d asked any CSO if they thought that most of their staff would be working remotely 6 months ago, they would have thought you were bonkers! Yet, as I write this blog, I find myself in a very strange and yet interesting time. When faced with an impossible situation the only thing that’s left to do is the impossible. The new daily norm is 'moving from video conference to video conference', my last meeting today was with the National Cyber Security Centre (NCSC) where they presented to the group on Bring Your Own Device (BYOD), something that government and CNI would have rarely conceived of a few months ago, but today guidelines are issued on how to deliver these services safely.
The world has changed in the last 6 months and there is no going back, digital transformation for remote working has been accelerated by 5+ years and that is only going to be great for business, if carried out correctly.
Rush Rush
We discussed the global remote networking trends in April where we identified an increase of more than 40 percent for Remote Desktop Protocol (RDP) and 30 percent for Virtual Private Networks (VPN). This rush to deliver ‘something’ enabled business to quickly establish methods of remote working, however many of these solutions are not as robust as they should be.
Now that we’ve had over 3 months to reflect on the remote working evolution, it’s time to take stock of the benefits and evaluate embedding this securely into the business operations for the future.
Selecting the Right Solution
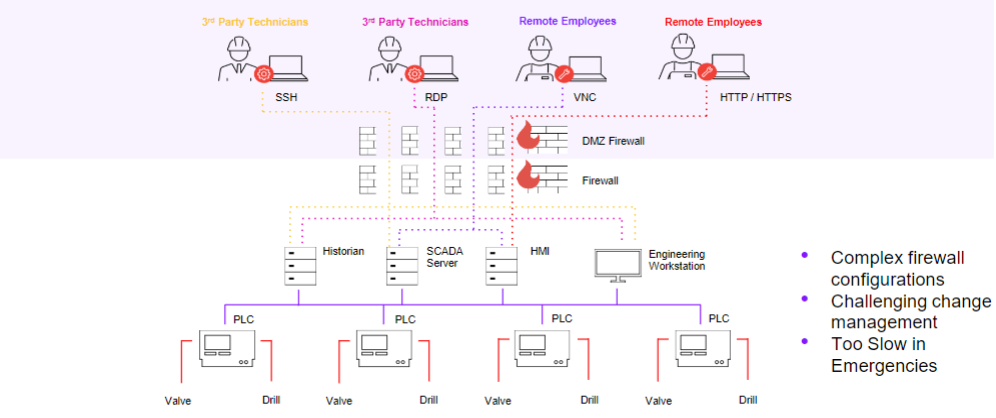
With traditional VPN’s there is a complex set of firewall rules that need to be in place, often this is managed by the IT department and internal process can be complicated to onboard 3rd party vendors. Changes to plant infrastructure and users can quickly outdate firewall rules and permissions. Furthermore, if your manufacturing operation is across multiple sites this complexity may be multiplied.
VPN access allows direct connectivity to the target network, this is a potential vector for threats to be introduced into the secure operational environment.
The NCSC advise for Cyber Assessment Framework (CAF) security principal B.4 - System Security that “at boundaries with higher security zones where it's necessary to import and trust data from a lower security zone, where possible: in a DMZ convert the data into the simplest appropriate alternate protocol, to create a "break" that makes protocol based attacks more difficult”.
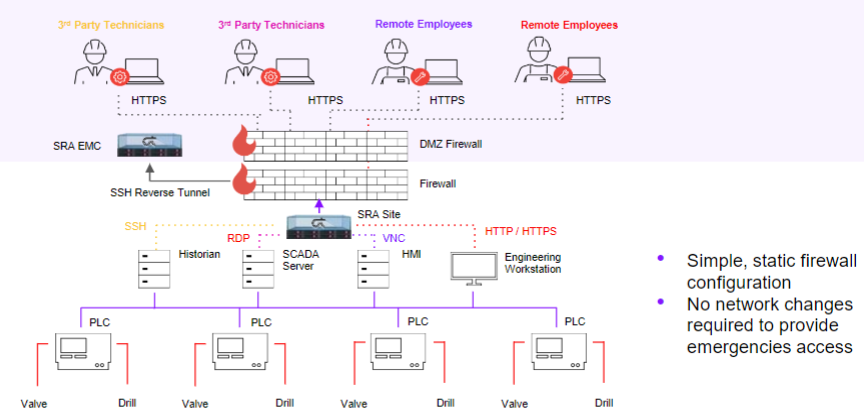
Our partners at Claroty have addressed many of the security challenges with Secure Remote Access (SRA) which takes account of how OT personnel operates ‘on site’ while working ‘off site’. With compliance in mind, SRA helps to address a number of challenges that are faced by our customers who operate in regulated industries and need to comply with the NIS Directive and CAF in principals such as B2, B3, B4, B5, C1 ,C2* and D2* (* in conjunction with Claroty Continuous Threat Detection (CTD)).
Firstly, all connections are terminated at the point of entry and re-established via a reverse tunnel northbound from the OT zone into the Enterprise zone using a single encrypted TCP port. Connections are presented clientless through a HTML5 browser as a graphical ‘window’, breaking the connection into OT through the use of an isolated RDP, Web, SSH or VNC connection, all which originate from the Claroty appliance. Access is monitored and recorded so all user interactions can be retained for compliance, as well as being validated in real time by an administrator who can terminate sessions at any time.
Robust authentication is delivered with 2 factor authentication, this can be integrated with Microsoft Active Directory or 3rd party solutions using SAML2. Passwords can be vaulted so sensitive OT credentials are never exposed to 3rd parties. For extremely sensitive systems, this allows for up to 6 factor authentication if challenged at the edge, gateway and then device.
Simple OT-Centric Workflows
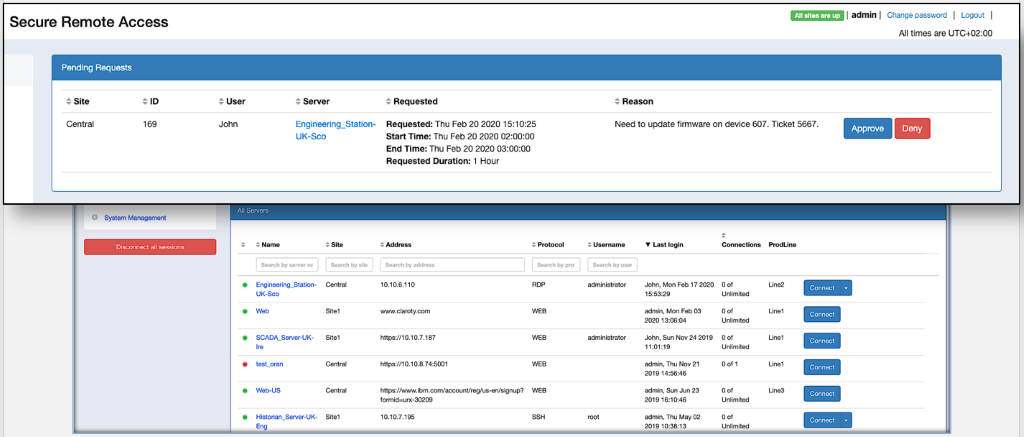
SRA is designed to be used by OT staff, who are best positioned to authorise remote access to their facilities. The interface is tailored to the needs of OT remote access, lowering training requirements and the likelihood of configuration errors.
Unlike traditional remote access solutions, authority to connect can be managed with ease enforcing administrator approval, this can be time based and revoked at any time. If work was being undertaken physically on site, there would be a permit to work, time slot allocated and personnel may be escorted while on site. Why should this be any different virtually?
A mixture of timed based, adhoc and always accessible systems can be easily configured using users and groups as well as assets to suit all use cases.
Where direct access is needed to interact with plant hardware such as a PLC’s from a vendor supplied device, the concept of an ‘Application Tunnel’ can be deployed which allows a single TCP port to connect to a single asset, again with strong 2 factor authentication and the right to terminate the connection at any time.
Claroty bridges the industrial cybersecurity gap between IT and OT environments, with solutions that scale from a single site to global operations and are deployed in all seven continents and operate within all OT verticals.
Times are Changing, are You?
There has never been a more important time to have robust and easy to manage remote connectivity for OT. Recent events have made us revisit out business continuity plans and review the provisions that were put in place for global pandemics. While we hope and pray there will not be a second wave, it's impossible to tell when these tools will be needed again in anger or, seeing the benefits that they brought, if they will ever be revoked. What is certain is that it’s been proven we can adapt to change and prosper.
Staying Ahead
SolutionsPT are Claroty preferred UK and Ireland distributor and platinum partner with over 30 years Industrial IT experience combined with in-depth knowledge of OT architectures. By taking a ‘secure by design’ approach, we deliver a long-term security architecture that is inherently secure against threats and can achieve compliance within your industry.
Further Information
- Claroty Secure Remote Access is purpose-built for operational technology remote access, providing a simple to use, OT-aware solution that supports distributed deployments and is secure by design. See here how these principles are being met.
- If you have 3 minutes to spare to find out more about SRA and how it can help you, then we have just the video for you here!
- If you would like to know more about Claroty SRA then download the latest datasheet here.


