Control systems have huge amounts of valuable business data flowing through them and access to this can be transformative for an organisation. However, there’s a problem as the Transmission Control Protocol (TCP) and Internet Protocol (IP) weren’t designed to be secure - they were only designed to ensure communications work.

In this blog, we’ll highlight why this is a major problem, the real-world consequences it’s had as well as the right approach you need to take to secure your system to avoid repercussions.
- The Existing Problem With Control Systems
- The Real World Consequences It Can Have
- How to Secure Your System and What to Avoid
The Existing Problem With Control Systems
With so much data, you need to ensure the data is accessed in a way that doesn’t compromise the system as it can result in kinetic consequences in the real world.
Programmable Logic Controls (PLCs) were also designed to replace relays. Their primary function is to service IT/OT while ethernet was an afterthought. More importantly, though, they weren’t designed to be secure. A big problem that can have huge consequences.
So, why is this a problem? Well in today’s climate especially, hackers will have even more time on their hands and can be an even bigger nuisance than normal. It’s a profitable business for them with a 1,425% ROI for ransomware alone.
Then you need to think about malware as a service (MaaS), hacking as a service (HaaS), crimeware as a service (CaaS), fraud as a service (FaaS)...the list can go on. But there’s also the risk of losing intellectual property with insecure systems and also corporate espionage to consider.
Any one of these, or even a combination, can be hugely detrimental. If data falls in the wrong hands, it not only damages your brand name but also your reputation as it highlights your failure to secure your systems and subsequently your data. That’s something a handful of organisations have realised the difficult way.
The Real World Consequences It Can Have
The more connected industrial systems become, the more vulnerabilities they’re exposed to. With poor security methods in place, hackers can be successful which leads to greater consequences.
Stuxnet
It’s assumed that the development of Stuxnet began in 2005, five years before it was identified which highlights how long this has been an underlying issue. It had devastating effects on industrial control systems (ICS) as it escaped the digital realm to wreak havoc on equipment.
This attack changed the industry, as an attack against an ICS infected over 200,000 computers and caused 1,000 machines to physically degrade. To understand the true impact of this attack, this was an alleged nation-state attack which damaged centrifuges used for uranium enrichment.
Triton
Dubbed 'the world’s most murderous malware', Triton is a rogue code that can disable safety systems remotely which were designed to prevent catastrophic industrial accidents. If the attack was successful, then the world-case scenario could have resulted in the release of toxic hydrogen sulfide gas or caused explosions - putting lives at risk.
It was the first time code was deliberately designed to put lives at risk when it brought a plant to a halt in 2017.
Norsk Hydro
35,000 employees affected. 40 countries impacted. Locked files on thousands of servers and PCs. Over $71 million in financial impact. That’s the result of the ransomware attack on the aluminium producer, Norsk Hydro. All of that damage started three months earlier when an employee unknowingly opened an infected email from a trusted customer.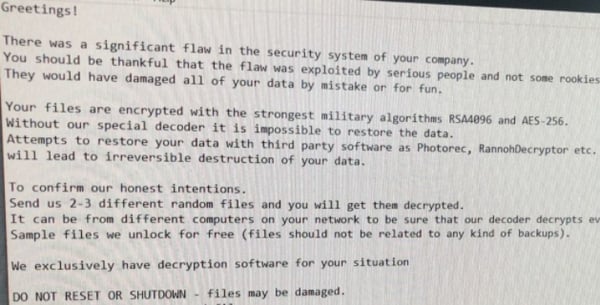
That innocent move allowed hackers to invade the IT infrastructure, plant the virus and gain a foothold in the system to control the entire IT infrastructure. These attacks are just the tip of the iceberg, there are many more cases where poor system security results in major consequences:
- Ekans: Ransomware seeking to do real-world damage by shutting down vital ICS indefinitely by targeting 64 different software processes unique to and common on ICS.
- Night Dragon: Another infamous case which involved the theft of sensitive information from operational oil and gas field production systems, including that from an ICS.
- WannaCry: Although not a primary objective, it managed to affect ICS including Windows computers managing industrial control software. It affected ICS and OT environments through a lack of patching and incorrect segmentation, creating a favourable environment to paralyse processes.
- BlackEnergy: A Trojan used to conduct DDoS attacks, information destruction attacks and cyber espionage. Attackers began deploying SCADA-related plugins to victims in 2014 in ICS and energy markets around the world.
Petya, Troconix, CrashOverride - the list can go on. The highest risks are ransomware attacks which can leave a devastating impact. To avoid potentially being in a similar situation, a standard anti-malware solution isn’t enough. Instead, you need to focus on using a multi-layered approach with security embedded in the process.
How to Secure Your System and What to Avoid
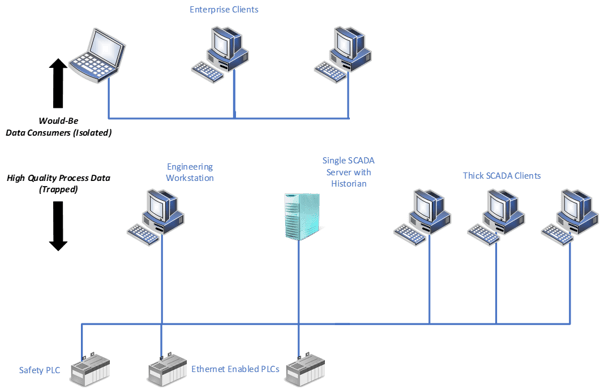
Part of the problem begins with control systems being isolated from the enterprise. Take a look at the isolated example below. There’s a lot of high-quality process data available - but the illustration shows that it’s trapped at the control layer so if enterprise users want to access the data, how could they do it?
What Not to Do
Before diving into the correct approach you should adopt, here’s a quick rundown of what you shouldn’t do.
- Join networks together without thinking about cyber controls.
- Dual homing so engineers can access PLCs via the engineering workstation from their own desk. This is a known attack vector as it enables attackers to pivot between networks.
- Make a direct connection to SCADA/historian for reporting. This offers no protection against viruses/malware from an enterprise level. There’s also no protection against excessive load from the enterprise side and it can cause upset on the control system.

The Correct Approach
- To secure the control system, follow a standard such as ISA/IEC62443.
- Create a Cyber Security Management System (CSMS). Here’s a process to define the cyber policy for your organisation:
- Initiate.
- Risk analysis (high-level and detailed).
- Establish the policy and raise awareness.
- Select and implement countermeasures.
- Maintain.
- Consider security risks at the design phase.
- Implement recommendations as required.
- Treated cybersecurity as an ongoing issue, rather than a ‘one-and-done’ task.
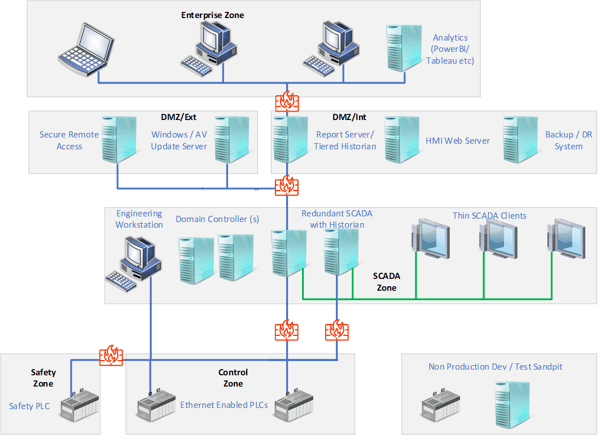
Now here’s a look at an example network with added security. You’ll see that after instigating a CSMS, there are now a set of zones defined to segregate different system components. This also sets boundaries and pathways, in and out of each zone which can be controlled and direct connections to the control system are removed.
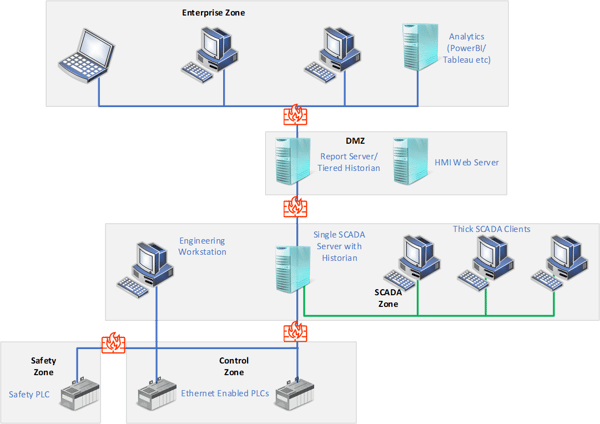
The CSMS is risk-led and procedure-driven. Your system will undoubtedly look different based on the output of your CSMS and how your organisation approaches risk. The way data is delivered to the enterprise layers also changes as there’s an ability to query an offline data source with a business intelligence tool, such as PowerBI or Tableau.
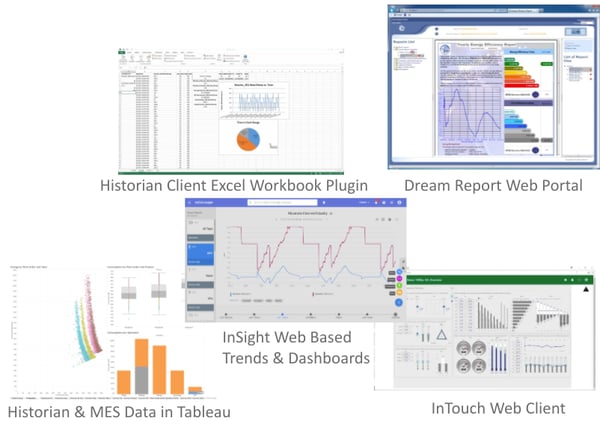
Visibility of reports in a single web portal can be scheduled or run ad-hoc as required. Manual data browsing and quarrying can be complete without affecting the production system and along with a live view of plant graphics, it can integrate with enterprise programs, such as Microsoft Excel.
That doesn’t have to look like the final solution either. You can improve on it and secure it further with added resilience by:
- Using a domain controller to control access and the security policy of the control system.
- Implement secure remote access via a single controllable channel for technicians and vendors.
- Migration to thin SCADA clients to reduce the attack surface.
- Addition of redundant SCADA server.
- Use of update service for patching and A/V updates with own DMZ.
- DR system for instant recovery if the control system fails.
- A non-production sandpit to test out changes or patches before applying them to the production system.
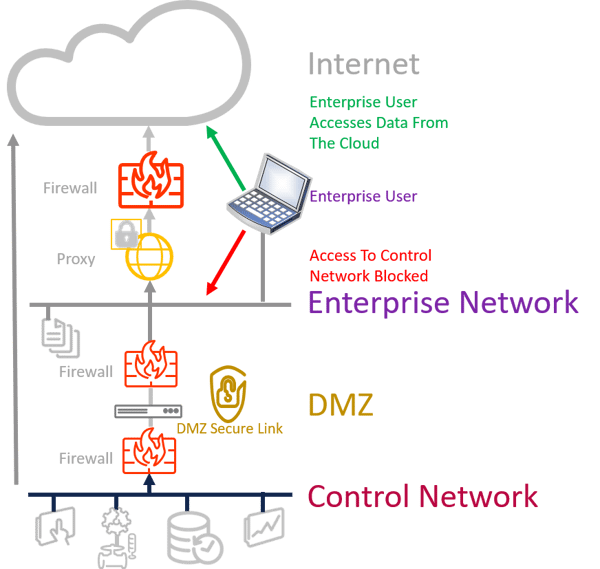
In some cases, you might not want to maintain a new reporting system in your organisation. If that’s the case, a cloud approach could work better. Here, the system is patched and managed by others and new features are added automatically. The data is internet-accessible and it’s a great choice for putting multi-site data aggregation into one repository.
With this approach, there’s also no direct link between the control network and the enterprise user and it can be secured with technology, such as a data diode if mandated by the CSMS. From a price perspective, it’s a subscription model so there’s an OPEX cost.
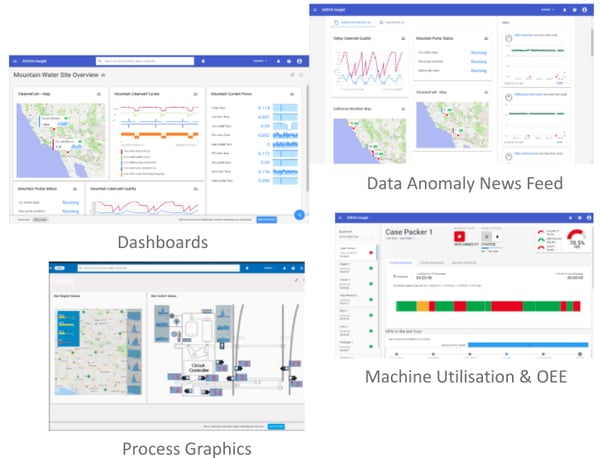
The data delivered to the enterprise layer can then be viewed via dashboards, process graphics, data anomaly news feeds and more.
Remember, security is a layered approach. Vulnerabilities will continuously be discovered, best practice methodologies will advance and your plant network will also evolve. To ensure your control systems stay protected and don’t fall to any of the rising ransomware attacks, it’s important to bring two vital business functions together.
Your Guide to Converging Your IT and OT Teams
IT and OT teams can no longer keep their distance. Aligning the two can result in cybersecurity benefits and streamline your processes. For the essential information on IT and OT convergence, make sure to download our free guide. It highlights the benefits you’ll reap, why it’s the right decision and much more.
Click below to get your copy.


