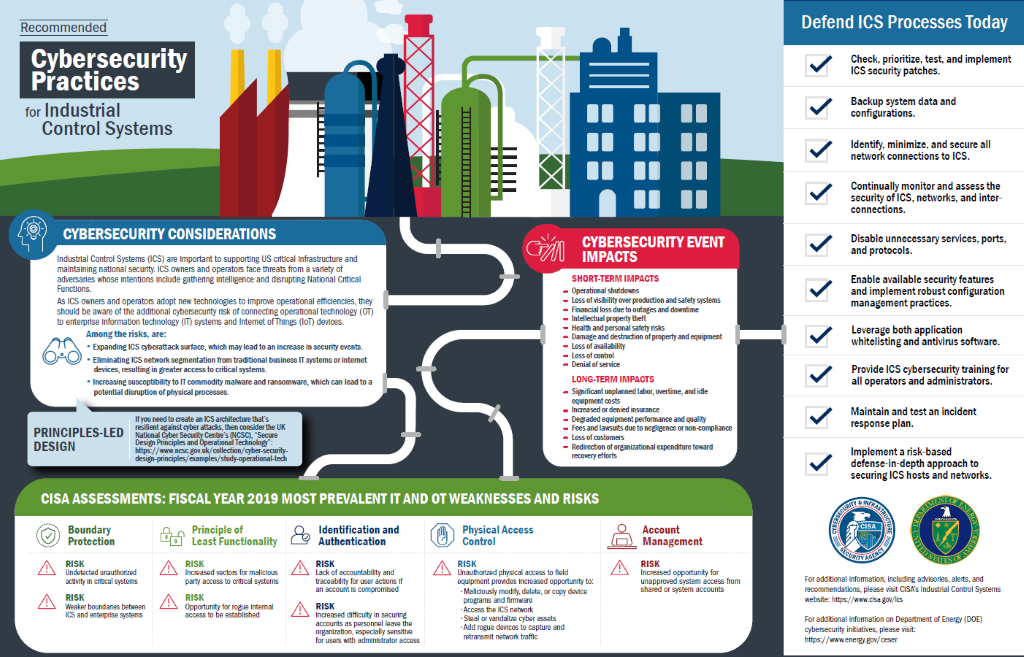
The Cybersecurity and Infrastructure Security Agency (CISA), the Department of Energy (DOE) and the UK's National Cyber Security Centre (NCSC) have just released the Cybersecurity Best Practices for Industrial Control Systems, an infographic providing recommended practices for industrial control systems (ICS). This forms part of wider information set that provides best practice guidance on a range of ICS security topics, including updating of Antivirus in an Industrial Control System.
Industry Insight
Guidance from CISA on how Antivirus (AV) software should be updated in industrial environments recommends a secure network architecture which places the ICS Antivirus, Windows Server Update Services (WSUS), and Patch server(s) in the control LAN within a demilitarized zone (DMZ) at Level 3.
Since the ICS DMZ is typically isolated, updating servers within this zone may require a level of engineering effort, this may include manually downloading the update using a process called “SneakerNet” and importing data using removable media. Another method which is more automated is to connect to a replica or slave server within the Enterprise zone.
From a defence in depth approach, having a single AV engine throughout the Enterprise and within the ICS environment is not the most robust approach, and its important to consider the need to include support for legacy operating systems like XP and Server 2003 if these are also present.
When considering OS patches, connecting to an upstream Windows Update Server also has some limitations. Control is delegated to the primary server for patch collection which is often managed by the IT department responsible for the whole Enterprise. This can unfortunately lead to patches for operating systems and applications being obtained that are not required within the ICS environment.
One size doesn’t fit all.
Is there a Better Way?
Manual updates as per CISA guidance has the potential to introduce complexity and a level of risk if not correctly managed. Malware can be transferred via removable media especially without additional compensation controls being in place, such as a ‘Sheep Dip’, USB scanning, USB media restrictions and multi-spectral scanning of content.
Where systems are synchronised between the enterprise and ICS DMZ, connection orientation may need to be bidirectional or initiated southbound into the ICS DMZ from the enterprise creating a wider attack surface. While there may be a 1 to 1 relationship between the child server in the ICS DMZ and the parent update server within the enterprise, this relationship is often 1 to many from within the enterprise zone.
Different Requirements
ICS networks often contain legacy systems which may not be supported through a single security suite, or worse, these assets have no protection whatsoever if the operating system is no longer supported.
Organisations that have robust change control processes may also mandate that updates and AV signatures have to be fully tested and hash validated before deployment which provides a window of risk between updates being current and protection being deployed. This constant cycle of obtain, validate, deploy, all of which takes time and effort and offers little to no protection to zero-day threats until signatures or patches have been successfully deployed.
ICS networks are not the same as IT networks, so why do we treat them the same for endpoint protection?
Customer Requirements
While the security needs for IT and OT endpoints are broadly aligned, i.e. the need to protect the endpoint, the similarities take a different path thereafter and been identified by our customers as:
-
-
- Having low resource utilisation on the host
- Require minimal maintenance and updating
- Be effective on ‘air gapped’ and ‘partially connected’ networks
- Provide protection to current and legacy systems
- Protect against known and unknown threats
- Identify root cause analysis
- Compensate for operating systems and applications that are no longer being patched
- Restrict and control the use of removable media accessed on OT assets
- Have the ability to interface with enterprise event collection tools
-
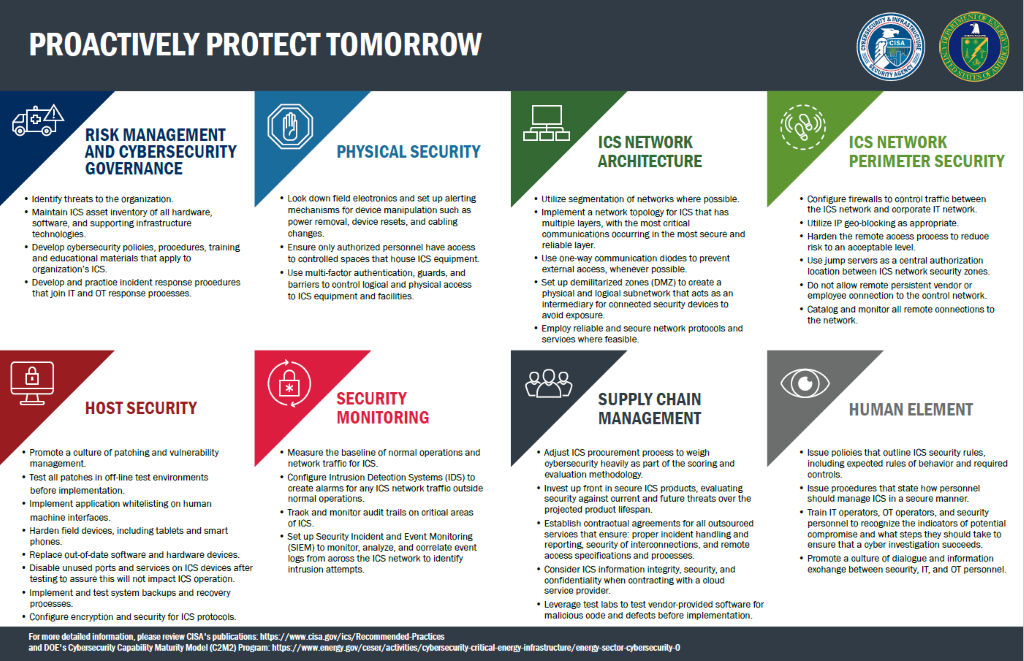
OT Focused Approach
We have discussed this in depth with our blog Antivirus that works for OT where we challenge the norm and addressed the shortfalls with traditional AV by taking an approach that is led by Artificial Intelligence (AI) which can co-exist with traditional security solutions for a defence in depth approach.
SolutionsPT partners with Blackberry Cylance who have a proven track record with endpoint security with CylancePROTECT which is deployed in Government, Critical National Infrastructure and Military environments around the world. These key sectors understand the need for a different approach to security where signature updates are no longer required.
A malicious application can change its signature through recompiling, what stays consistent is the behavioural indicators which identify that file as a risk through threat profiling, these are consistent regardless of its signature or hash value.
Zero Day Protection - The Predictive Advantage
AI threat profiling gives a proven predictive advantage of up to 33 months over known, unknown, and zero-day malware. CylancePROTECT is capable of preventing threats that did not exist when the AI model was first created.
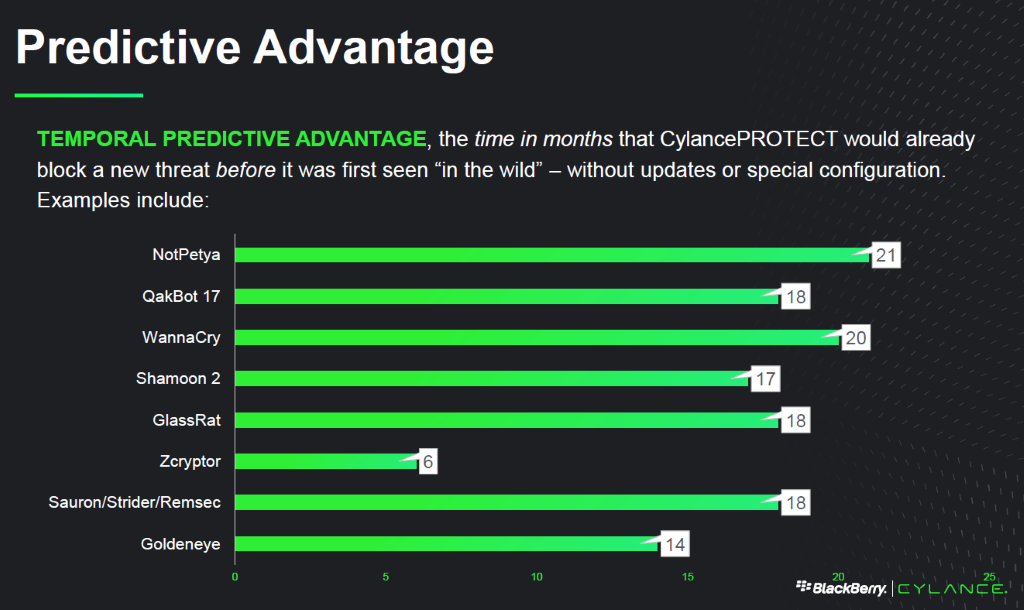
In practical terms, this indicates that regular updates to CylancePROTECT are not always necessary which is ideal for ICS environments. Updates to the AI model is ongoing and generally sees releases every 6 months which better suits planned downtime and maintenance schedules.
SE labs undertook an independent study of CylancePROTECT predictive advantage, the report is available here.
Protecting Today
At SolutionsPT we closely monitor challenges faced with our industrial customers and review innovations within the IT market, selecting best in class solutions which are suitable for OT environments. Our solutions are tested to ensure they are compatible with all the core products we offer so you can be assured they can successfully co-exist, saving you time and effort.
Proactively Protecting Tomorrow
Blackberry Cylance is a mature and a proven AI technology which is deployed to over 14 million devices. CylancePROTECT is a component of the Blackberry SPARK platform which delivers Unified Endpoint Security (UES), affording the same level of protection to tablets and mobile devices. Choices taken today can help protect assets of the future as well as legacy devices of the past.
If you are ready to see what your incumbent protection products may be missing or just want to break free of the constant upgrade cycle associated with legacy Antivirus, we can provide a no obligation 30-day proof of concept. Why not let the technology speak for itself?
#solutionspt #otsecurity #otcybersecurity


